Carmel Academy offers the best Logistics & Shipping courses in Kerala.
Carmel Academy offers logistics & shipping courses in Kochi Kerala. We offer Logistics Diploma, Post Graduate Diploma, Advanced Diploma courses for +2 Holders, Graduates and Post Graduates who wish to pursue their career in LOGISTICS. It is a well acclaimed logistics Training Institute based in Kochi, Kerala, focusing mainly in guiding and assisting them to accomplish their dreams in this very booming and high remunerative global career.
Logistics, Shipping and supply chain management are core corporate functions to virtually all the industries in various countries. In fact, ensuring an efficient logistics system can provide a competitive edge to the exports of the country as also a tremendous boost to a country’s economy making imports available at cheaper prices. So it is having lot of high remunerative job opportunities in this field.


Secure your Future
Carmel Logistics Academy
Kochi, Kerala

Convocation Ceremony
at Carmel Academy
Kochi, Kerala

Motivational Session by
Mr. Deepak Boharpi
Chairman - Madni International Logistics
We are affiliated to



Courses We Provide

Logistics and Shipping along with MBA
Duration : 2 Years
Eligibility : Any Degree & above

Logistics and Shipping along with BBA
Duration : 3 Years
Eligibility : +2 & above

Professional PG diploma in Logistics and Shipping
Duration : 1 Year
Eligibility : +2 & above

Diploma in Logistics and Shipping
Duration : 6 Months
Eligibility : +2 & above

Certificate in Logistics and Shipping
Duration : 3 Months
Eligibility : +2 & above

IELTS Training
Duration : 3 Months
Eligibility : +2 & above

Geriatric Nursing Course
Duration : 6 Months
Eligibility : +2 & above
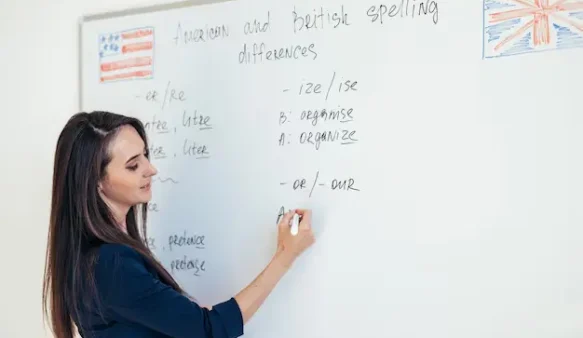
Spoken English Course
Duration : 3 Months
Eligibility : 10th & above
Carmel Logistics Academy
Join the best Logistics & Shipping institute in Kerala - Carmel Academy
Carmel Academy offers logistics & shipping courses in Kerala. We offer Logistics Diploma, Post Graduate Diploma, Advanced Diploma courses for +2 Holders, Graduates and Post Graduates who wish to pursue their career in LOGISTICS.
We research the market to deliver up-to-the-minute, quality, and actionable insight that is presented when and how you want it. It’s time to alter the talent in your business, regardless of your professional level, and we have the insights you need to do it.

Why choose Shipping and Logistics courses from Carmel Academy?
Internal trade involves controlling and moving items from their source to their destination, which is where shipping and logistics play a vital role.
Therefore, for those who are interested in transportation and trade management in India, a career in shipping and logistics is the best choice. If you choose the best diploma programmes and the best certification programme, shipping and logistics in India can be a very useful career option. The business offers a variety of opportunities.
Objective Of Shipping and Logistics Courses
- To provide expertise in shipping and logistics on a practical level.
- Participate actively in the development of India's commerce infrastructure.
- To increase Indian exporters' ability to compete in the international market.
- To build right skills and groundwork required to develop Indian Economy.

Student Testimonials
Listen to what our students have to say ...




Our Students are Placed at



















Still not convinced?
Get more details about our Logistics & Shipping Courses in Kerala
Carmel Academy offers logistics & shipping courses in Kochi Kerala. We offer Logistics Diploma, Post Graduate Diploma, Advanced Diploma courses for +2 Holders, Graduates and Post Graduates who wish to pursue their career in LOGISTICS.
Why join Carmel Logistics Academy?
# 1 Rated Shipping & Logistics Courses in Kerala

TOP RATED LOGISTICS TRAINING INSTITUTE IN KERALA
syllabus Covering all aspects of shipping & Logistics.
COMPLETELY JOB-ORIENTED PRACTICAL EDUCATION.
Well qualified and highly experienced Faculty.
Professional briefing/coaching at site through industrial visits
INDUSTRY EXPERIENCED TRAINERS wITH YEARS OF EXPERIENCE
AC Smartclass rooms will support you to know the best.
Knowledge based grooming and personally development.
CERTIFIED BY INTERNATIONAL AND DOMESTIC BODIES
Frequently Asked Questions
Carmel Academy offers logistics diploma, postgraduate diploma, and advanced diploma courses for students who wish to pursue a career in logistics and shipping.
Carmel Academy provides up-to-date market research and insights to help students stay ahead of the competition. The institute offers practical training to develop expertise in shipping and logistics, as well as the opportunity to participate in the development of India’s commerce infrastructure.
Shipping and logistics are core corporate functions for virtually all industries in India. Ensuring an efficient logistics system can provide a competitive edge to the country’s exports and boost the economy. A career in shipping and logistics can be highly remunerative and offer a variety of opportunities.
Skills required for a career in shipping and logistics include organizational and problem-solving skills, effective communication and interpersonal skills, and knowledge of trade laws and regulations. Carmel Academy offers courses designed to provide students with the necessary skills to succeed in this field.
Shipping and logistics offer a wide range of job opportunities, including supply chain management, transportation management, logistics management, and inventory management. Graduates from Carmel Academy’s logistics courses can pursue careers in various industries and sectors.